A Cloud Guide: The Benefits Of Cloud Computing

Cloud computing saves time and money

It saves money as the company will require a smaller IT staff and small businesses may actually only need an IT consultant they can call when needed. It will vastly lessen the costs of buying new hardware, upgrading hardware, maintaining hardware and purchasing additional storage space. It saves on physical storage space as all files will be stored in the cloud. No bulky file cabinets or storage rooms are needed. All upgrades and maintenance are performed by the cloud storage provider. Paper and printing costs will be eliminated or vastly reduced.
Cloud computing brings efficiency with BYOD

Because of the BYOD movement, Samsung implemented Knox Security into the Samsung S4, a trend that's sure to take off among other phone manufacturers. This added security feature enables the phone to be split into two separate sections- one for personal use and one for business use. This means that all company data remains secured in the business section while personal SMS messages, photos and other data remains free from the IT department's security monitoring.
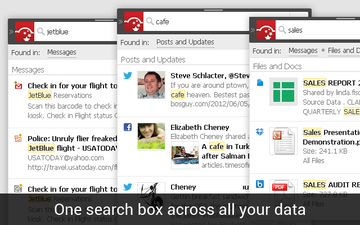
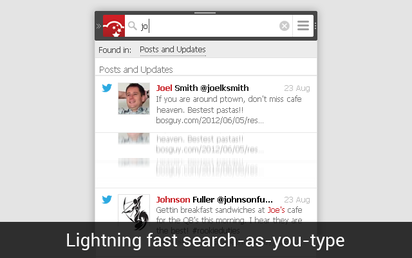
Cloud Computing offers easier sharing and searching

Cloud computing makes searching for files and folders a quick and simple process. Forget searching through huge storerooms with thousands of folders, all files within a cloud storage account can be searched within seconds. There are even apps such as CloudMagic that allow users to search across many different cloud services. This works well if your company is using multiple cloud storage providers such as Google Drive, SkyDrive, Dropbox and more.
Cloud computing provides stronger security

Cloud computing offers complete security from natural disasters such as fire, flood, hurricanes, tornadoes, etc. If a company's physical location is destroyed by a natural disaster, all company files and folders remain intact, safely stored away in cloud servers. And if you’re worried about the cloud storage servers getting hit by a natural disaster, there are cloud storage backup services such as cloudHQ, which provides a continuous backup of all data. It can even sync files across a variety of cloud storage providers.
The cloud is here to stay
- Is Cloud Computing Right for Your Small Business? (staples.com)
- Cloud Computing Pros and Cons (techneckhc.wordpress.com)
- Top 10 Cloud Computing Questions & Answers (staples.com)
- Advances of Cloud Computing in Business Development (cloud.dzone.com)
- Cloud computing modernizes education in China (zdnet.com)
- More small businesses are adopting cloud computing in Ireland - Microsoft/Amárach Cloud Index (siliconrepublic.com)
- What is cloud computing? (tankjustin.wordpress.com)
- A Cloud of Suspicion: Legal Issues Surrounding Cloud Computing (nclawlife.com)
- The aaS in Cloud Computing (hobbycollegecareer.wordpress.com)
- How Cloud Computing Has Empowered The End User (datacenterknowledge.com)





 RSS Feed
RSS Feed
